The dark web is often viewed as a hidden space tied to hackers and illegal activity, but that image only tells part of the story. In reality, it also supports legitimate users such as journalists avoiding censorship, activists operating under surveillance, whistleblowers exposing corruption, and cybersecurity researchers tracking cybercrime.
Unlike the surface web accessed through browsers like Chrome or Safari, the dark web runs on encrypted networks that provide anonymity. The Tor Browser will remain the most reliable and widely used way to access it. However, entering the dark web is only the first step—finding trustworthy and relevant information can be difficult without proper tools.
Without a reliable dark web search engine, users are left navigating endless random links, increasing the risk of scams, malware, illegal content, or legal trouble. A trusted search engine helps users discover valuable resources safely while minimizing unnecessary risks.
In this guide, we cover the 10 Best Dark Web Search Engines, explaining how they work, who should use them, and how to stay safe while navigating the dark web.
Detailed List of Best Dark Web Search Engine Today
Dark web search engines offer a variety of services, and all have a different level of risk associated with them. Here are the best dark net search engines of 2026 and what they offer:
1. OnionFind
- Visit: onionfind.com
OnionFind is a secure, anonymous way for individuals to find and discover .onion websites on the Dark Web. The search engine offers a unique and very ethical way to access the Dark Web. Journalists, activists, individuals interested in protecting their privacy, and people located in regions where certain content may be restricted will find this platform helpful.
The search engine has a continually growing, frequently updated, and curated catalog of different categories where users can find numerous types of content available on the Dark Web.
The search engine also offers a zero-tracking infrastructure:
- No tracking via cookies
- No search logs
- No behavioural tracking.
OnionFind is an example of a tool that uses the dark web to provide access to a search engine without tracking or storing user activity, which sets it apart from many other tools on the dark web. It has both a clearnet official address (onionfind.com) and a .onion address.
Who should use OnionFind?
OnionFind was designed to be particularly helpful for people such as:
- Reporters working in countries where there are restrictions on the press.
- Whistleblowers attempting to submit sensitive information.
- Activists attempting to organize events anonymously.
- Researchers who want to explore the Tor ecosystem.
- Individuals who live in countries where access to the Internet is limited.
Additionally, OnionFind supports various organizations that focus on privacy protection, including:
- The Tor Project
- Electronic Frontier Foundation
- Privacy International
- Access Now
Alignment with these types of organizations helps to position OnionFind as a legitimate privacy-protection tool rather than a criminal access point.
How to use OnionFind safely:
To use OnionFind in a responsible manner, please do the following:
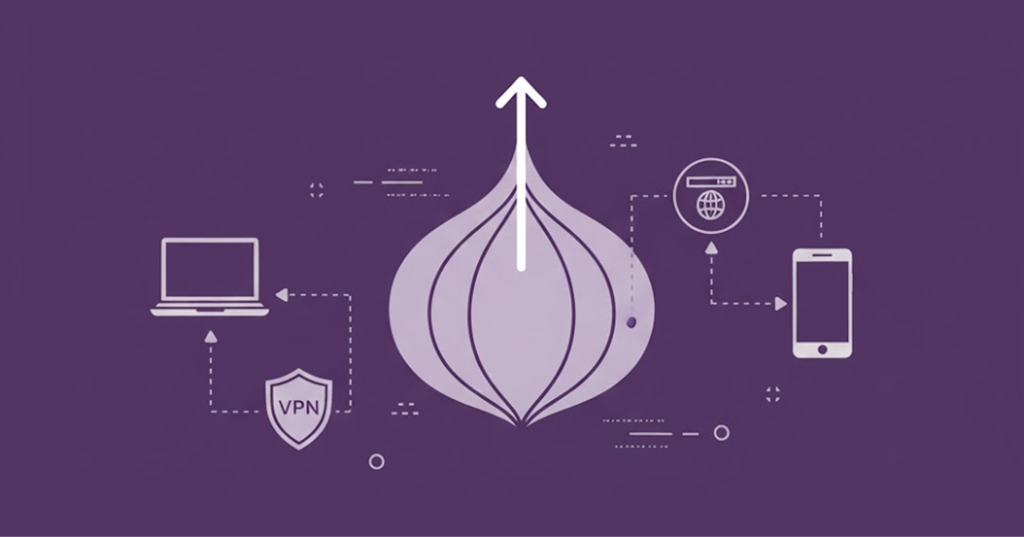
- Connect to your VPN prior to using the Tor network.
- Open the Tor Browser.
- Connect to OnionFind’s .onion address.
- Be cautious at all times!
2. DuckDuckGo
- Visit: duckduckgo.com
DuckDuckGo is not a search engine/website for the Dark Web; it’s one of the most common tools used on the Tor network for searching.
It’s unique .onion services allow users to search the standard surface web while remaining anonymous on the Tor Network. The benefits are:
- Prevention of tracking users’ IP addresses
- Preventing Browser Fingerprinting
- Preventing the profiling of users’ search behaviors
This is an extremely useful and beneficial tool for journalists, activists, researchers, and Political Dissidents.
DuckDuckGo has a very strict “no-logs” policy, as well as a “no-tracking” policy, ensuring:
- Searches will not be stored
- Identity does not form a profile
- Activity cannot be sold to Advertisers
When used with Tor, the search engine becomes one of the most secure methods for people to search for information anonymously on the internet, not just the dark web.
Best use cases:
- Researching anonymous journalism
- Conducting political studies in censored countries
- Performing security research, and wanting to remain private on the surface web
- Anyone wanting a Google-style search without being monitored
Advantages of DuckDuckGo:
- No tracking or logs
- Has a familiar/easy user interface
- Enables “Google-like” anonymous searching
- It is very fast/stable.
Disadvantages:
- Does not crawl dark websites
- Limited to only “surface web” results.
3. Ahmia
- Visit: ahmia.fi
Ahmia is built in partnership with the Tor Project as a means of supporting the ethical and legal use of resources from the dark web. Users will see a very basic platform, but an active filter prevents illegal activity and other unsafe sites and profiles from being displayed.
Ahmia is among the most intuitive dark net search engines, as it strives to combine user-friendly features with both security and usability. Unlike many dark web search engines, Ahmia does not connect with unfiltered content right away. Instead, it blocks:
- All known illegal sites
- All infected links
- All information related to abuse and abuse-related information
Unlike many dark web search engines, Ahmia provides a distinct balance between privacy and accountability in its offerings.
Additionally, its structure and user experiences are similar to those offered by search engines on the surface of the internet; therefore, for users who are new to both Ahmia and other tools to access the dark web, this easy-to-use and familiar design should prompt overall ease of learning to use these tools.
Privacy & openness:
The Ahmia application has an open-source codebase. The open-source nature allows security researchers, those who develop software, & contractors who work independently to review the operations of the Ahmia app as well as what vulnerabilities exist within the software. In the dark web environment, trust is a key component. Ahmia’s number one asset is its transparency.
The search engine specifically chooses to focus on a higher degree of security and makes trade-offs, including not having one of the largest indexes currently operating on the dark web.
Best audiences:
- Those interested in anonymity network academic research
- Cautious journalists performing investigative journalism
- First-time Tor users
- Advocates of privacy who are trying to minimize their exposure to harmful content
Limitations:
- Smaller index than uncensored search engines
- Some deeper or underground websites may be excluded
While Ahmia has a lower risk factor because it filters heavily, users must still exercise complete operational security through the combination of using Tor and a virtual private network (VPN).
4. OnionLinks
- Visit: onionlinks.com
OnionLinks has an extensive indexing of .onion sites, is one of the major uncensored indexers, and one of the oldest. Users interested in using OnionLinks should be more experienced, wish to be able to explore deep within the dark web, and have raw, unfiltered access.
Advantages:
- Tremendous index of .onion links available.
- Along with a large index of .onion links, OnionLinks is also one of the fastest indexes on the Dark Web.
- OnionLinks has a no-log policy, meaning that it does not track users.
- OnionLinks is one of the oldest operational indexes still in existence.
Disadvantages:
- No content filtering to prevent access to illegal, disturbing, or adult content.
- For a new user, the risk of encountering illegal and disturbing content is very high.
- OnionLinks is not recommended for novice users.
5. Recon
- Visit: recon.com
The objective of Recon is to gather and verify information regarding the products being sold on the Darknet, along with the seller’s identity (individual or legal). Similar to the traditional marketplace, the data collected will help law enforcement agencies and cybercrime investigators understand what product is sold by whom, where they can be found, and how the seller has been rated on darknet marketplaces.
Target audience: individuals investigating cybercrime and cyber fraud, law enforcement agencies, cybercrime journalists/analysts, and individuals who perform research in order to develop their own knowledge (researchers within the cybercrime field).
Recon collects:
- The characteristics of vendors.
- The types of products they are currently offering.
- Ratings and reviews associated with specific products.
- Their transaction patterns.
As a result, Recon enables users to:
- Compare individual vendors’ selling accounts across different marketplaces.
- Evaluate a vendor’s reputation by utilizing user ratings.
- Report any ongoing fraudulent activity.
- Track the release dates of products sold on the darknet.
Who Uses Recon?
Recon provides:
Indispensable intelligence for individuals and organizations in the field of cyber threat intelligence,
- Recon is useful for agencies that enforce diverse laws while carrying out their investigations into any crime or fraud that takes place on the internet.
- Journalists/analysts who share news on the same crimes over the web also gain a lot by using Recon.
- Academic researchers studying the dark economy.
Because it provides unique insights and information on how the dark economy functions in real time, it serves as a resource to the cyber threat intelligence community.
6. TorDex

- Visit: tordex.com
TorDex has built its reputation as one of the largest collections of .onion websites, which has allowed users to connect with others and share information across multiple channels. The search capabilities of TorDex are powerful and have led to many discoveries on the network.
Active Discussion Forums, Privacy Protection Websites and Marketplaces, Community Sites, Underground Forums, etc. Unlike other search engines like Ahmia or OnionFind that focus on Safe Surfing, the search results from TorDex contain no limits whatsoever on content; therefore, discovering content can also pose challenges for certain users.
TorDex has the following features:
- Queries based on keywords can be executed quickly
- Easy to navigate
- Follows a structure similar to a standard surface web search engine
Since the engine utilizes a user interface similar to traditional search engines, individuals who are already familiar with a traditional search engine will experience fewer difficulties utilizing TorDex.
Use cases:
- General overview of how dark web ecosystems work.
- Discovering newly created .onion sites.
- Individuals who have a clear understanding of the risks associated with the dark web.
- Individuals who are studying cybersecurity or performing Intermediate research.
It is imperative to exercise strict operational security measures while using TorDex. The use of TorDex should only occur when there is a specific purpose for utilizing it.
7. VormWeb

- Visit: vormweb.de
VormWeb offers a slightly different approach compared to other dark web search engines, because, in addition to providing searching capability, it also provides ongoing education and Privacy-Focused Journalism.
It functions as both a directory and a platform for learning for those interested in:
Along with the articles and news about Tor and Anonymity Networks, VormWeb regularly publishes information about Dark Web Trends and current safety warnings. Therefore, VormWeb is not just a search tool; it creates a learning space for those who are concerned about privacy when using the internet.
Some of the best uses of VormWeb would be:
- First-time dark web users looking for context about Dark Web Usage and meaning.
- Students learning about Internet Censorship.
- Individuals who want to learn and search at the same time.
Advantages of VormWeb:
- The interface is very simple to navigate on and this is why even beginners can be comfortable on it.
- Developed using Open-Source Software.
- Offers educational blog articles and privacy-related news.
- It combines searches to educate users.
Disadvantages of VormWeb:
- Provides an abundance of unfiltered content.
- Not all results have undergone verification.
- It still poses a significant risk.
Even though VormWeb’s main purpose is education, it still displays uncensored results, and users may see unauthorized or malicious links. Additionally, users must follow their OpSec guidelines on all searches.
8. Haystack
Visit: haystacksearch.org
Haystack is a community-supported dark web platform; its main functions include search, forum, and user interaction. It is ideal for those users looking for insights from the community, as well as for peer discovery.
Haystack’s Advantages include:
- Tools created for peer-to-peer discovery,
- A community for sharing links, and the
- Ability to find lesser-known sites.
Disadvantages of Haystack include:
- Slower speed
- Limited index compared to bulk engines
- The credibility of community recommendations can vary
On the surface web, reputation systems and moderation greatly minimize the risks associated with conducting business on the internet.
Trust is very much a fragile concept with the dark web. Haystack provides a platform for users to add to the existing pool of available resources by:
- Providing safer sites
- Providing scam warnings
- Providing current mirror sites
- Providing an environment for operational security discussions
While automated indexing can be effective, the human factor often carries greater weight.
Best uses for Haystack:
- Accessing community-approved resources.
- Learning from long-term Tor users.
- Using non-commercial dark web resources.
9. DarknetSearch
- Visit: darknetsearch.com
DarknetSearch operates on the premise of “doing one thing well.” Rather than having analytics or forums or a filtering layer, it concentrates fully on speedy, straightforward searches for .onion websites.
For people who dislike complicated platforms but need fast retrieval of .onion links, DarknetSearch is one of the fastest available options.
All about performance
DarknetSearch’s design allows it to load quickly over relatively low bandwidth connections, such as those used by Tor, with its minimalist layout greatly reducing:
- The use of large scripts
- The use of features requiring large amounts of resources
- The chances of being tracked
Best application cases:
- Quickly identifying specific resources located on .onion
- Advanced users already have an idea of what they are searching for
- Rapid reconnaissance of well-known keywords
10. Torch
- Visit: torchsearch.org
Torch is the leading service for indexing the entire dark web marketplace, as well as all vendors doing business within those marketplaces.
The advanced capability of Torch makes it the go-to platform for law enforcement and other organizations that conduct deep investigations into the dark web.
Strengths of Torch
- Massive dark web marketplace indexing service.
- Advanced vendor and product filtering capabilities.
- Advanced capability to enhance privacy associated with completing transactions.
- Established service with a long history of operation.
Some of the weaknesses associated with using Torch include:
- The potential for exposure to the dark web
- A strong focus on illegal commerce
- The big risk of being exposed to both the legal and ethical issues associated with operating a business on the dark web.
The advanced filtering capabilities of Torch have permitted users to fine-tune their searches by numerous factors, eliminating any extraneous information. When users search for specific vendors or products, they can use the filtering tools provided by Torch to select vendor location, vendor rating, and the type of product being searched for.
They can also select the region of shipping and the activity level of the market from which they are attempting to obtain the product. It also provides tools to enhance transaction privacy, including bitcoin mixing services.
Torch falls within a 3-ring Category we see with illegal commerce, financial crime, and international law enforcement interest. Simply looking at a dark web marketplace exposes a user to undercover operations, surveillance, scams, and malware.
Therefore, users should only use Torch for high-level cybercriminal investigation/research/intelligence monitoring. Academic/investigative journalism using Torch and other dark web marketplaces must be done under strict legal direction.
Picking a Good Darknet Search Engine for You
In 2026, a major portion of darknet usage is for illegal acts. The other half can be identified for legal acts as well. The good acts include privacy shields, discovery gateways, intelligence platforms, educational tools and early warning systems, and much more.
When using the following search engines, select from the best dark web search engines and do your homework when selecting your option. If you require excellent security, then select Search Engines like OnionFind, DuckDuckGo, or Ahmia.
If you are looking for the best place for hard-to-find in-depth intelligence, then look at Recon and Torch. The Haystack and the VormWeb are both available to those people who want human insight along with technical discoveries.
These services each have a different purpose for their users and have differing levels of risk tolerance; as such, how you use either service has a direct impact on your safety.
The Function of Dark Web Search Engines Today
Today, dark web search engines function much differently than they did five years ago. In 2020, a dark web search engine was just another directory; however, the size of the dark web is so large that many unindexed web pages exist.
Today, these search engines facilitate anonymous interaction and censor-resistant activity, as well as provide crucial cybersecurity intelligence. The key lies in the foundational role of dark web search engines combined with the multi-layered functions they offer.
1. The Purpose and Function of a Dark Web Search Engine
All dark web search engines have the same basic purpose: they provide users with access to encrypted websites of criminal organizations on the dark web.
However, the method of accessing these websites varies depending on the purpose of each search engine. Users will have these types of dark web search engines to choose from:
- General Discovery: Ahmia, TorDex
- Intelligence Gathering: Recon, Torch
- Privacy-First Access: OnionFind
- Community Centered Discovery: Haystack.
Dark web search engines are a must-have; without any of them, or their absence, would make finding your way around the dark web almost impossible.
A major advantage of dark web search engines is that they are unregulated; no one organisation manages them, nor is there a single way to catalogue everything within them
2. All Dark Web Search Engines Focus on the Aspect of Privacy
“We do not share our personal data with the government, hackers, advertisers, or anyone else.”
These dark web search engines allow users to research and gather information on a wide range of topics without being concerned about being watched or retaliated against for their actions.
3. An Additional Key Element of Dark Web Search Engines is Their Specialization
Most dark web search engines are specialized (whereas Google is an all-encompassing search engine).
While Google strives to index everything available on the Internet, many dark web search engines appear to focus on a more niche target audience of users.
Examples:
- Recon & Torch are focused primarily on underground markets.
- VormWeb combines search with privacy-centred journalism.
- OnionFind provides a lawful way of indexing content through curation.
4. Community and Human-Based Verification
On a hybrid platform like Haystack, human curation plays a vital role. Users share with each other verified links, scam warnings, dead-site updates, and security advice.
Since automated crawling is unreliable and inefficient in the dark web’s environment, human verification acts as a substitute for traditional methods of establishing trust.
5. Risk Navigation and Filtering
Although search engines do not provide true security systems, they can act as warning systems. Platforms like Ahmia and OnionFind attempt to filter known illegal content, deprioritize malicious domains, and limit the probability of exposure to unwanted content.
Additionally, the use of organized content allows for greater control over where a person may navigate and decreases the chances of randomly wandering into dangerous areas.
6. Information, Education, and Digital Freedom
Lastly, modern dark web search engines could be used as:
- An Educational Resource for research.
- A Gateway to scientific research.
- An Infrastructure for Digital Freedom.
The Risks of Using Dark Web Search Engines
The dark web has inherent security risks. Regardless of how “good” any particular dark web search engine might be, it is still a risk to use a dark web search engine.
No “Tech” has ever been considered the “holy grail” for its user. However, if users are aware of the dangers present within the dark web, they can better prepare themselves against these risks.
Here is a list of the main dangers that all users of dark web search engines should know about; these include:
Malware and Phishing Attacks
A number of “.onion” sites are intentionally designed to distribute trojans, install spyware, steal encrypted credentials, and hijack cryptocurrency wallets.
In addition, several phishing sites closely mimic legitimate onion services visually. A single erroneous click can place your computer at great risk.
Illegal and Disturbing Content
There is a lot of legal content on the dark web; however, there is also illegal content on the dark web that will eventually be found by search engines, including:
- Black market items
- Stolen information
- Fraud-based services
- Extremely unsettling images, videos, or graphics
If you unintentionally see illegal content, it can have psychological effects on your mental being, but it also may be against the law in certain places.
Scams and Fraud
Cryptocurrency fraud and scams are really almost everywhere. There are fake markets where people build sites just for:
- Collecting deposits;
- Disappearing with those deposits and never providing anything in return
- Rotating through different URLs.
Even users who are experienced frequently fall victim to cryptocurrency scams and fraud.
Legal Tracking and Sting Operations
Tor and anonymity are good friends, but not sufficient to give you absolute privacy. When law enforcement does things such as:
- Traffic correlation attacks
- Undercover marketplace stings
- Metadata analysis
- Infrastructure seizure
Simply browsing or using the dark web is generally viewed as permissible by law, but engaging with illicit services is a different situation altogether and could subject you to severe legal consequences.
Dead Links and Infrastructure Instability
As previously stated, it is typical for sites on the dark web to experience infrastructure failure from one of the following:
- Law enforcement action
- Hosting service closing down
- Exit scams from the operators of the sites
- Misconfigured servers
As a result of these types of infrastructure failure, you will notice a large number of dead links, constant rotation of mirrors, and the fact that there will not be lasting trust relationships.
How to Access the Dark Web Safely
When choosing which search engine to use to reach the dark web, the type of security you have set up to protect the pathway itself must be up to par.
If you attempt to enter the dark web without having secured yourself, it is similar to entering a high-risk area without protective measures
Steps for Using Tor today
The steps we have for you below will make sure you stay safe on Tor:
Step 1: Buy yourself a paid & dependable VPN.
Use a reliable paid VPN prior to opening your Tor Browser. A VPN will provide a layer of protection by:
- Encrypting all of your internet data.
- Hiding your true IP address from your Internet Service Provider (ISP).
- Preventing the monitoring of your internet activity by people on your local network.
Your ISP sees only a VPN connection and cannot detect your Tor usage.
Avoid free VPNs at all costs because they come with serious security and privacy risks. Many free VPNs:
- Log users’ activities.
- Sell their users’ browsing history.
- Leak users’ actual IP addresses.
- Offer a weak level of encryption.
Using a paid VPN and focusing on security is not optional.
Step 2: Download and install the Tor browser
The Tor Browser is currently the most reliable and most used dark web browser. It allows you to route your internet connection through many nodes operated by volunteers while encrypting your information along all routes.
To view most dark websites, you’ll need the Tor Browser software installed and its security levels set to “Safest.”
Disables the following features:
- JavaScript
- All Types of Media
While using JavaScript and Media Players makes using certain sites more convenient, the risks outweigh the benefits.
Also, you must use strict operational security (OpSec) practices. Without strict operational security, anonymity is not possible.
Never:
- Use your real name
- Use a personal e-mail address
- Reuse passwords
- Link to another account on the surface web
- Never download files unless absolutely necessary
The dark web hosts a large amount of malware disguised as documents, software tools, media files, and fake ‘super security’ utilities. Every file has an associated risk.
For a complete, step-by-step protocol that goes beyond tool setup, read our detailed guide on how to browse the dark web safely.
The Importance of Safe Searching on Dark Markets
Safe searching on dark markets will continue to be one of the most important issues in internet security by 2026.
No longer is the Dark Web a hinterland of obscurity. It has grown to become one of the leading armies in the ongoing digital resistance movement against the encroaching digital surveillance architecture.
As such, the need for the safe and secure conduct of all users remains paramount, and future risk management will remain a priority for all users.
Data Breaches Have Now Become a Daily Threat to Millions of Users in All Industries
Every year, billions of usernames/passwords, medical records, and financial information are sold on/accessed through hidden marketplaces each year.
According to industry estimates, there will continue to be hundreds of millions of compromised users’ credentials residing on underground marketplaces today.
For businesses, this means:
- Not only can employee credentials already be circulating, but attackers can also misuse customer data
- Ransomware attacks usually begin when leaked credentials surface on dark websites.
For individuals, this means:
- Your previously forgotten logins (usernames and passwords) from many years ago may still be bought and sold in the present time on dark web marketplaces. This is just one facet of the broader threat landscape detailed in our guide on understanding dark web dangers and risks. Specialized search engines provide access to the dark web, offering cybersecurity teams and researchers an effective means of locating credentials and determining how they became exposed.
This way, they can take action before the hackers cause any significant damage to a company’s network or an individual’s identity.
Cybercrime Has Evolved Into a Service Industry
Today’s cybercriminal operations range from ransomware gangs and exploit brokers to fraudsters and initial access sellers, to name just a few. These are all legitimate business-like operations with their professional members and skilled trades, just like any other legitimate business today.
The cybercriminal underworld is now a large market that offers many different types of products and services using a combination of encrypted and/or hidden services, including the following:
- Zero-day exploits
- Hacked servers
- Malware toolkits
- Stolen identities
- Bank Account Information
- Employee Access to Corporate Networks
A great deal of the planning that goes on associated with major cyberattacks takes place long before the news media ever reports on any of the events.
The sooner you can identify and respond to cybercriminal actions, the higher the probability of preventing or reducing any harm.
Anonymity Protects Both Innocents and Criminals
The Tor Network and other anonymity technologies were originally developed to promote free speech and protect privacy. The Technologies serving these purposes continue to serve these same purposes today for:
- Those of us who work under an authoritarian regime
- Human Rights Organizations
- Political Dissidents
- Whistleblowers who expose corruption
However, besides offering positive protection for these legitimate groups, anonymity also provides protection for illegal activities, and has been shown through research studies that much of the content produced on the Dark Web is composed of illegal and harmful content.
The safe dark web search engines act as a buffer, giving legitimate researchers and users the ability to remain within ethical and legal requirements while minimizing their risk of encountering harmful content.
Increasing Pressure for Law Enforcement
There has been a large increase in the number of operations around the world aimed at addressing Dark Web activity. According to industry reports, in 2026, large established operations like Operation RapTor resulted in:
- Hundreds of Arrests
- The seizing of millions of dollars in assets
- Shutdown of numerous large dark web marketplaces
The Dark Web consistently evolves. Each time a market is shut down, new markets are developed under different names, meaning that search engines that haven’t been updated will become ineffective.
Likewise, search engines that have been reliable must be updated to ensure they remain safe.
Dark Web Intelligence Has Become an Everyday Standard in Security
The process of monitoring the dark web has now become part of “business as usual” for cybersecurity professionals. For example, during penetration testing and threat searching activities, they will look for:
- leaked credentials for corporations
- mention of corporations on illicit sites
- stolen intellectual property
- plans relating to advanced persistent threats
By collecting this type of intelligence, an organization can gain an extremely unique view of its organization as viewed by an attacker.
It is critical that you complete this type of research using only legal and secure ways (not through reckless browsing).
Extra Precautions to Stay Safe on the Dark Web

The first thing to note is that using a dark web, underground search engine in 2026 without paying does not guarantee safety.
It’s important to remember that just because you are using a top dark web search engine today for free does not mean you’re safe.
Personal behavior is the foremost determining factor of how secure you are while on the dark web; tool choice only plays a secondary role.
To ensure that every user remains as safe as possible while exploring the dark web, here is a full safety framework every user should employ.
Do Not Provide Any Personal Information
Never share the following with anyone while on the dark web:
- Real name
- Home address
- Phone numbers
- Personal email addresses
- Job details
- Social media connections
Linking personal identity with online information is one of the most common ways that people get compromised on the dark web.
Do Not Use Any Credit Cards or Bank Accounts
Almost all financial transactions carried out on the dark web are either made with a cryptocurrency like Bitcoin, Monero, or Litecoin.
Using traditional financial accounts exposes your actual identity, your banking relationships, and your transaction history. Even trying to link a debit or credit card to your activities on the dark web is very dangerous.
Trust No One Until You Verify Their Identity Yourself
Do not trust anyone until you have validated their credentials and established contact with them. Many people who sell something there will lie that they have good reputations, even show where their customers said good things about them (lies, of course), and even show that their community supports them wholly, and these are nothing but fallacies.
So, you can’t allow them to fool you at all when doing anything with them (other people on the dark web)
Turn Off Scripts, Disable JavaScript, & Set Your Security to the Safest Mode
When using the Tor browser, ensure you have configured the security settings to the highest level, blocked the execution of JavaScript (utilising the NoScript extension), & disabled all media playback.
Scripts are a common method used to:
- Fingerprint your device
- Deliver malware
- Leak your IP address
Do not download files
Malware coming from the dark web is often included within:
- PDF files
- ZIP files
- Media content
- Software setups
If downloading is necessary, it must only be done within a fully functional isolated virtual machine.
Use long, unique passwords every time
All accounts that you create on a .onion site should:
- Have long but random passwords
- Do not have the same password as used on the surface web
- Have their passwords kept in an encrypted manager
Due to the widespread use of the same password for many different accounts, your account may be hacked.
Utilize a VPN + Tor Together
Utilizing a VPN will protect you from:
- Monitoring by your ISP
- Surveillance by others on the same local network
- Traffic analysis from where you came from
- Utilizing Tor will provide this additional level of anonymity.
Do not enter the dark web through Tor while on your own direct connection.
FAQs
The simple answer is no. Google and Bing only search the ‘surface’ web and do not index .onion URLs, so you will have to access the dark web through a browser designed for use on the dark web (such as the Tor Browser).
Many of the dark web search engines will lead you to illegal black market sites, phishing sites, and malware-ridden websites. Most of the ones you find out there have bad areas, although they may have some good things going on as well.
Yes! People visit the hidden web to do many things, and that is not breaking the law. For instance, journalists might want to learn more about news stories as fast as they can using that space. The other group of people are researchers who may have other findings to do regarding how people share information through digital devices, how ordinary users can keep themselves hidden online, & how to enjoy the benefits of encryption technology. Cybersecurity professionals are not to be forgotten because they have an interest in the dark web as well.
The deep web and the dark web should not be confused. The deep web is made up of legal (but not publicly accessible) material, i.e., email accounts, banking services, and some corporate intranets, all of which can be accessed via search engines. The Dark Web has nothing to do with an index, meaning that you can’t find it anywhere on the internet. To find anything at all on the Dark Web, using the designated software is just what you must do.
No matter where you are entering from, accessing the dark net is not illegal. It only becomes illegal when someone partakes in purchasing illegal products, sharing illegal materials, or engaging in criminal acts for financial gain. Hence, a number of countries have strong opinions against the use of technology for anonymity, such as China, Russia, and Iran.
