Clearly, people keep seeking better ways to improve their online privacy. There are many reasons for this, such as government surveillance, snoopy ISPs, and hackers stealing data. The Tor network is one of the best options if you want to keep your browsing activities private. But, unfortunately, it provides only a single anonymity layer, which can expose some of your traffic, especially at exit nodes.
If used with Onion (Tor), a Virtual Private Network (VPN) will add an encryption layer to your Tor connection and keep your entire traffic completely anonymous. So, the Tor VPN combination is a dynamic duo that will strengthen your online security and privacy.
In this guide, we’ll give you a detailed explanation of Onion over VPN, the best VPNs for Tor, how Onion over VPN works, and more.
What is Onion Over VPN
We will have to look at how the different components involved function separately to illustrate how Onion over VPN works. Let’s first look at each briefly and then cover the duo.
What is a VPN?
Standing for a Virtual Private Network, a VPN is a technology that passes your web traffic through intermediary servers. It encrypts the connection between your device and the server, making it impossible to intercept your information. Also, the VPN will disguise your IP address when connecting to the server.
There are two primary ways you can get a VPN. First, you can create a VPN server, which is time-consuming and complicated. On the other hand, you can purchase a subscription from a VPN service provider.
The latter option has an extensive server network, allowing you to connect to any country you want. So, for example, you can be in the UK and connect to a server in the US. This will make you seem like you’re within the country, yet you are not.
What is Tor?
Tor is a free, open-source anonymity tool used to get around censorship to access all layers of the internet, including the dark web. To access the Tor network, you must use a Tor browser (which we’ve reviewed among other best private browsers), which is almost similar to regular browsers like Chrome and Firefox. Tor uses a sophisticated, multilayered security system to protect you from government surveillance, ISP monitoring, and cybercriminals. Tor’s multi-layered security protects your anonymity by:
- Encrypting your traffic: Tor routes and encrypts your data through a series of nodes to protect your anonymity.
- Masking your IP address: Tor hides your actual IP address from third parties, making it difficult to target you.
- Blocking trackers: Tor isolates every website you visit to prevent third-party trackers from following you on every site you visit.
- Blocking fingerprinting: Tor Browser makes your digital fingerprint look similar to other users.
- Binning your history: Tor permanently clears all your browsing history after closing tabs.
The Tor network encrypts your data three times before routing it to a series of random volunteer-hosted servers until it reaches the intended website. This conceals your identity while giving you a digital fingerprint like other Tor users. Therefore, trackers cannot fingerprint you based on your device or browser information.
Additionally, Tor prevents anyone monitoring your internet connection from seeing the websites you visit and your physical location. It also changes your IP address and enables you to bypass geo-restrictions. Moreover, Tor allows you to access the dark web, which is the unregulated part of the internet. Also, it automatically deletes all your browsing history after closing the tabs to provide further privacy.
Is a Tor Browser Necessary to Access the Tor Network?
Regular browsers cannot open Onion sites hosted on the Tor network, so you must use a Tor browser. Additionally, you should subscribe to a VPN with an Onion over VPN feature and combine it with a Tor Browser for maximum anonymity. However, there are only a few VPNs that support Onion over VPN.
Onion Over VPN Explained
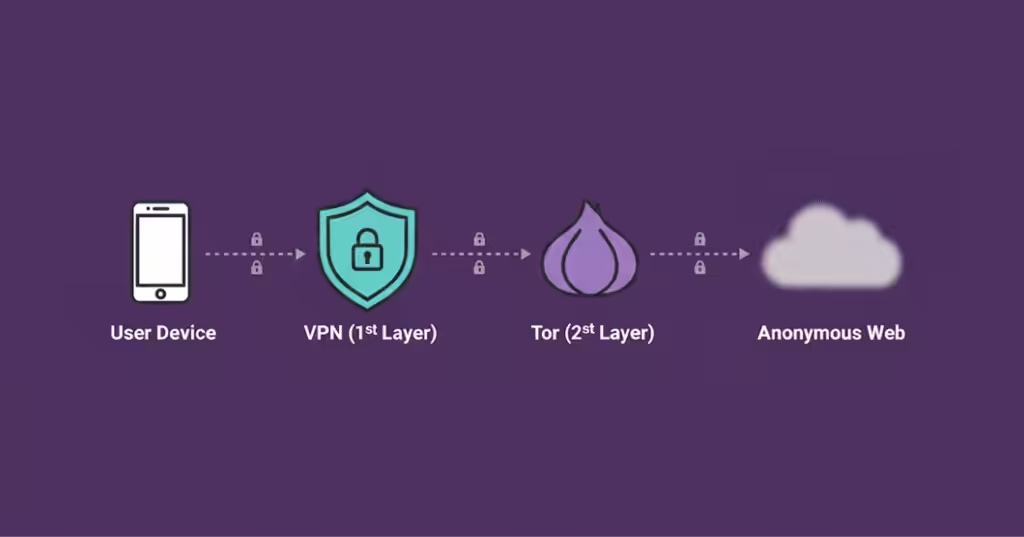
Onion over VPN is a security and anonymity strategy for accessing the Tor network. It involves connecting to a VPN before launching your Tor browser for maximum protection. The Tor network gives you anonymity, while the VPN provides privacy and security.
Combining the two technologies is ideal, especially when exploring the dark web. For this purpose, choosing the right VPN is critical (see our guide on the best VPNs for the dark web). Tor network anonymity may be compromised by third parties who dig deeper by running entry and exit nodes to reveal your identity. Therefore, you need a trustworthy VPN to protect your privacy and security.
Here is the path your traffic takes when using Onion over VPN.
- Encryption of data by VPN.
- Encryption of data by Tor.
- The VPN server receives data.
- The VPN encrypts your data and sends it to Tor, adding another layer of anonymity.
- Data is routed through a series of nodes, losing an encryption layer at each node.
- Data reaches its destination completely decrypted.
The response from the website takes this path.
- The application or website sends a response
- Tor encrypts the response
- Tor relays the data
- VPN encrypts data
- The data, which is already double-encrypted, is sent to your device
- Tor decrypts data
- VPN decrypts data
How to Set Up Onion Over VPN?
It is straightforward to use Onion over VPN. All you need is a Tor browser and a VPN service. A tool like Tortilla can be useful if you want to route your entire traffic through Tor. First, however, you will still need to use the Tor browser. The following steps will help you do it:
- Register for a VPN service. Choose a provider that has a strict no-logs policy and buy a subscription with an anonymous method. The idea is to leave as few bits of your identifiable data as possible. Our number one recommendation is NordVPN.
- Download and install the software on your device. Then, find a server with the highest speed and connect.
- Download and install the Tor browser. Then, open the browser and connect to the Tor network.
Once you complete the above three steps, your traffic will be protected by two encryption sources: the Tor browser and the VPN. Note that this would apply to your entire traffic if you use a tool like Tortilla.
Also, remember that the configuration involves many intermediary servers, so your connection speed reduces significantly. Therefore, you should use a VPN for everyday use and add the Tor browser for sensitive activities.
Is Onion Over VPN Safe?
Vulnerabilities in such a configuration can be attributed to the parties involved in the Onion network or the VPN.
When it comes to VPNs, some are more reliable than others. For example, you have to choose a no-logs service to be on the safe side. Unfortunately, some providers claim not to retain logs just to lure in more users. So, check for third-party audits by reputable firms and records of refusal to hand over data to authorities. A VPN that keeps logs is one of the impending threats to your privacy.
On the other hand, the biggest shortcoming of the Onion network is that anyone can create a Tor node. This means malicious actors can use rogue nodes to spy on your activities.
Therefore, your privacy will be based on two separate entities when you use a VPN together with Onion. The advantage is that the chain is longer if there is a point of failure or any other risk. For example, the VPN will encrypt the traffic that the Tor network cannot protect, like the ICMP. Conversely, your internet service provider (ISP) can tell when you use Tor. However, a VPN will make this impossible.
Safety Precautions When Using VPN Over Onion
The Onion over VPN provides you with the necessary privacy, security, and anonymity, but it cannot protect you from yourself. For instance, it cannot prevent you from submitting personal information to Onion websites, which can compromise your privacy.
Here are some precautions you need to take when using Onion over VPN:
- Think before you click: Many malicious users on the dark web plant viruses, malware, and scams. Generally, don’t click links that you do not recognize.
- Check URLs: Be keen to check the legitimacy and security of the URLs of the websites you visit. Check the address bar to ensure the URL starts with https:// and whether the name is correct.
- Install a robust antivirus: Get reliable, effective, and up-to-date antivirus software to detect and remove threats that could slip through your Onion over a VPN connection.
- Configure your Tor security and privacy settings: Tweak your Tor security settings to ‘safest.’ Some websites may not work, but it scales up your security and privacy. The ‘safest’ mode keeps you anonymous even if your Tor is hacked.
How Can I Safely Use Onion Over a VPN?

Setting up Onion over VPN is relatively easy, as you only need to connect to your VPN before launching your Tor browser.
The following steps show how you can safely use Onion over VPN:
- Subscribe to a reliable and trustworthy VPN that supports the Onion over VPN feature. We recommend NordVPN because of its efficient built-in Onion over VPN feature.
- Connect to a VPN server and ensure the server you connect to is near your physical location to boost connection speeds.
- Download and install the Tor browser on your device.
- Open your Tor Browser when still connected to the VPN server.
- Start browsing anonymously in an Onion over a VPN environment. Avoid sharing your personal information to protect your privacy.
Is a VPN for Tor Necessary?

The Tor Browser and VPN combination provides you with adequate privacy and security to safeguard your data and web traffic.
A standalone Tor Browser will anonymize your connections, but it’s easy to intercept the traffic at the entry and exit nodes. However, a VPN will seal all the gaps and keep you totally invisible with military-grade encryption.
The Tor browser is great for privacy, but it only protects the traffic by passing it through several nodes. As a result, any sites and apps outside the network can be easily exposed. This is why you need to add a VPN. It uses advanced encryption to offer robust security and anonymity, regardless of what you are doing online.
Pros and Cons of Using Onion Over Tor
These are some of the advantages of Onion over VPN:
- It makes it easy to access dark web .onion sites securely and anonymously
- This prevents your ISP from seeing that you are using a VPN
- Stops the VPN provider from seeing your traffic or the websites you visit
- Let you surf the internet anonymously and securely
- Flexibility to use a VPN with a normal browser for non-critical errands
- It thwarts the Tor exit node from seeing your actual IP address, but only that of the VPN server
At the same time, there are some cons of Onion over VPN:
- The VPN provider can see your actual IP address and that you are using the Tor network
- Apps and websites you visit can see your traffic emerging from a Tor exit node. In fact, they can block your connection or stop working altogether
- Compromised Tor exit nodes can potentially expose your data
- The combination of Tor and the VPN will significantly slow down your connection
When Can I Use Onion Over VPN?
The Onion over VPN approach is complex and emphasizes privacy, security, and anonymity. It is, therefore, ideal for transmitting highly sensitive information or bypassing geo-restrictions in countries with high censorship. It is commonly used by journalists and whistleblowers who want to remain anonymous.
Don’t use Onion over VPN if:
- Speed is important to your connection.
- You are accessing personally identifying sites like social media.
- You are casually browsing the internet.
Use Onion over VPN if:
- You are an activist, whistleblower, or journalist.
- Do not want to access the Tor network directly.
- You value anonymity.
Be cautious when using Tor because it cannot protect you from malicious exit nodes. The Onion over a VPN connection can also be extremely slow, so only use it when necessary. While the Onion over VPN is a perfect anonymity tool, it cannot guarantee 100% anonymity.
Double VPN vs. Onion Over VPN
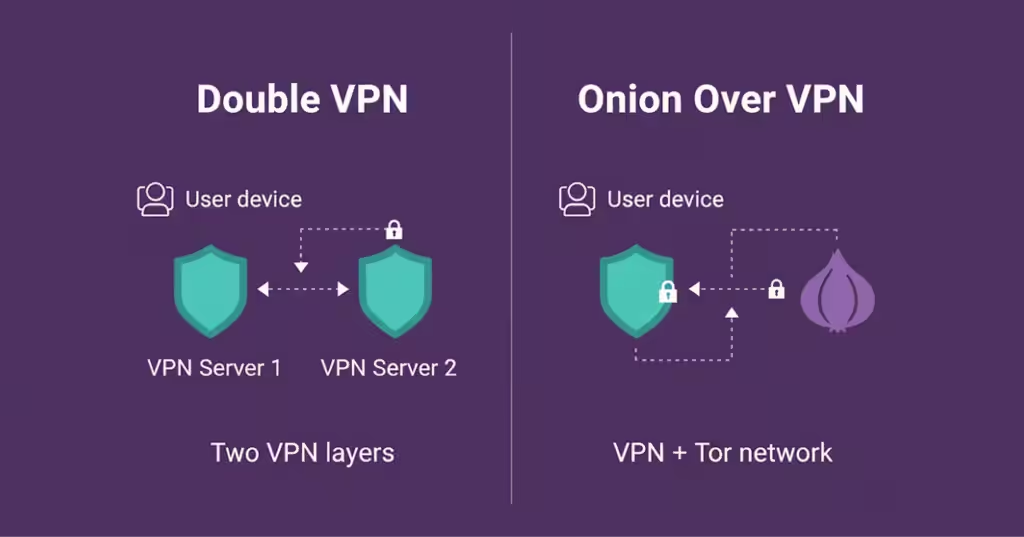
Remember that the Onion over VPN configuration isn’t the only solution if you want to increase your online anonymity. There is also an option to use several VPNs simultaneously. As a result, your connection will be passed through multiple servers, and your traffic will be encrypted twice.
Fortunately, different VPNs have integrated this feature into their apps, but name it differently. Some common names include double VPN, multi-hop, nested VPN, etc.
Moreover, you can try manually setting up the connection with two different VPN services. The problem is that there might be software compatibility issues. For example, the Windows operating system is susceptible to TAP driver errors. In addition, you may also need to pay for two different subscriptions.
Should I Use Tor Bridges Instead of a VPN?
There is an option to connect through Tor bridges when using the Tor network. Although bridges function similarly to relays, the benefit is that bridges are not public and aren’t included in the leading Tor directory. Unfortunately, it is tough to find them. Luckily, you can create them, but it’s complicated.
These bridges can improve your browsing experience significantly. Thankfully, they exist in different variants. For example, obfuscated Tor bridges will come in handy when accessing geo-blocked content in a country with heavy internet censorship, like China and the UAE, to name a couple. Most probably, your internet service provider (ISP) won’t block private Tor bridges.
VPN Over Onion VS Onion Over VPN
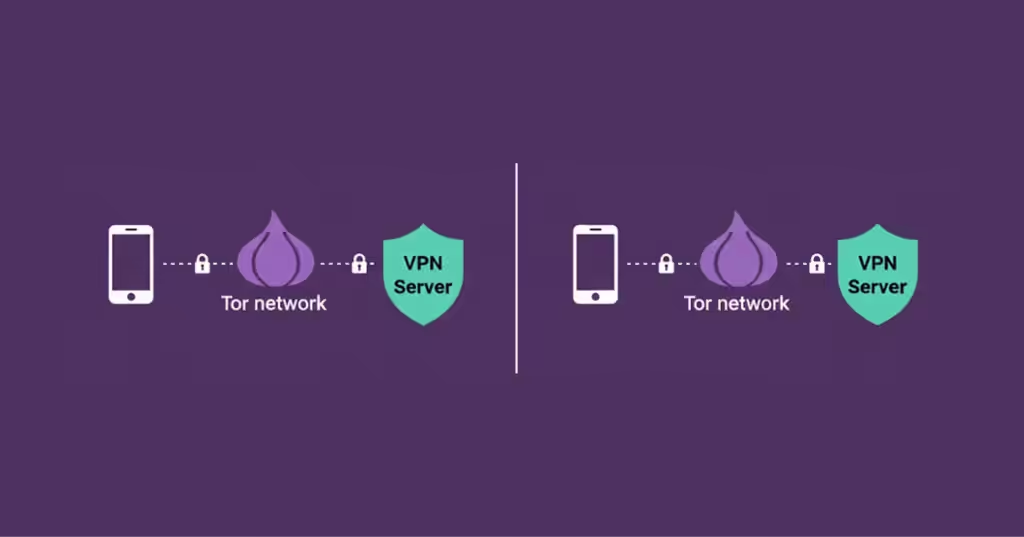
You can choose to connect your VPN before launching your Tor browser or start with the Tor browser and then connect to your VPN server. The first approach is called Onion over VPN, and the latter is called VPN over Onion.
VPN over Tor routes traffic through the Tor network first, then via the VPN’s encrypted tunnel. The connection undermines anonymity because the guard nodes can see your public IP address even though the exit nodes cannot see the contents of your traffic.
The table shows the advantages and disadvantages of VPN over Tor:
| Advantages | Disadvantages |
|---|---|
| Users can access websites that block exit nodes. A VPN kill switch can prevent data leaks and protect you against malicious nodes. | Users can access websites that block exit nodes. A VPN kill switch can prevent data leaks and protects you against malicious nodes. |
VPN over Onion is complex to set up, and you may need guidance from your VPN provider. Poor configurations may lead to traffic leaks, exposing you to countless online threats or undermining your anonymity.
How VPN Over Onion Affects Your Security and Privacy
Allows You to Access Websites that Block Tor Traffic
It is possible to access websites with blocked Tor IP addresses. This is because the websites receive a connection from a VPN server rather than a Tor exit node. Therefore, the website cannot determine whether the connection originates from the Tor network. Also, the IP address connecting to the website belongs to the VPN server and not the blocked Tor exit nodes.
Protects You Against Malicious Exit Nodes
In the VPN over Onion approach, the VPN is connected last, and therefore, it encrypts all the traffic from the exit node to the internet. Therefore, unlike Onion over VPN, the exit node can’t see your traffic’s contents. The exit node only knows you are connected to a VPN, but cannot see the websites you visit.
In this approach, the kill switch is very effective once the VPN connection drops. This prevents your information, such as your IP address, from leaking.
Government Agencies May Monitor Your Activities for Surveillance
When you connect to your Tor network directly without first connecting to a VPN, your ISP can see that you are using Tor and mark you for surveillance. Also, the Tor guard node can see your public IP address, which crushes all the efforts of staying anonymous.
Once security agencies like the National Security Agency (NSA) have your IP address, they can use their sophisticated technology to monitor your online activities.
Your VPN Can Monitor and Track Your Activity
Tor’s main focus is anonymity. So, VPN over Onion compromises your anonymity by allowing VPNs to access your web traffic and IP address. Also, some VPNs store identifying information on their servers, making your connection traceable. For this reason, Tor warns users against the VPN over the onion approach.
To Whom Does the Onion Over VPN Suit Best?

The Onion over VPN setup can help a wide variety of people due to its enhanced security and simplicity. These are some of the people who can benefit from Onion over VPN and why.
People With Sensitive Data
With the Onion over VPN setup, your ISP can see that you are using the configuration, but not your activities. This is because the VPN will secure your connection and prevent any third party from tracking what you are doing online. Therefore, you will get complete privacy and confidentiality to wander the internet freely.
Residents and Travelers in Countries With Autocratic Governments
The Onion over VPN setup is effortless to operate. A single click will route your traffic through the Tor network. Fortunately, several VPN providers have integrated the Onion network with their software. For instance, NordVPN offers this feature. The configuration will improve your online security and privacy so that government authorities cannot monitor your activities.
Journalists, Whistleblowers, and Political Activists
A VPN will encrypt your traffic and pass it through an encrypted tunnel, while the Tor network will improve your anonymity. This will enable you to browse anything on the internet privately and securely.
Conclusion
Using either the VPN or the Tor browser as a standalone service has advantages and downsides. Both options will encrypt your web traffic, but they cannot offer complete anonymity because of how they function.
The best solution is to combine forces and use Tor together with the VPN. Besides getting double encryption, the combination will solve inherent privacy issues. NordVPN is our top recommendation because of the dedicated Onion over VPN feature, strong encryption, and blazing-fast speeds.
FAQs
Although Tor is associated with the dark web, it is a perfectly legal network, and anybody can use it. On the other hand, VPN is widely accepted globally except in a few countries. Therefore, there is no problem using both of them to improve your online security and privacy.
Yes, Tor does need a VPN to work. However, using a VPN with Tor reinforces your privacy when visiting the dark web.
Many free VPNs claim to offer quality services, but you should avoid them. This is because most free VPNs employ inadequate security measures that cannot keep you safe. In addition, they generate income by selling users’ data and injecting malicious ads.
First, you have to look for your IP address before connecting. Then, after connecting with Tor, check again whether it has changed. If not, know that your Tor isn’t working.
Both configurations serve different purposes. However, Tor over VPN is much easier to set up and requires no technical skills. Conversely, VPN over Tor is a bit difficult to configure and has poor as well as poor performance.
Using both Tor and VPN slows down your connection because both technologies have to encrypt your data and route it through a series of nodes to achieve the desired anonymity. The encrypted data must also be decrypted upon reaching its destination, which consumes time again. Consider connecting to a nearby VPN server to improve connection speed.
Tor is short for ‘The Onion Router,’ also known as Onion. It is a technology designed for anonymity, housing dark web sites, also known as .onion sites.
